
Identity Theft Protection

IDENTITY THEFT involves someone taking your personal information without your knowledge to commit fraud or theft. According to the Federal Trade Commission (FTC) identity theft costs Americans billions of dollars every year. It is estimated that as many as 9 million Americans have their identity stolen each year. Victims can spend hundreds of dollars and countless hours trying to repair their credit and good name. The latest trend involves thieves taking advantage of the current economic situation by targeting job seekers, by establishing fake online job sites.
- Financial Identity Theft.
- Driver's License Identity Theft.
- Criminal Identity Theft.
- Social Security Identity Theft.
- Medical Identity Theft.
- Insurance Identity Theft.
- Child Identity Theft.
- Synthetic Identity Theft.
The FTC recommends a deter, detect, and defend approach to protect yourself from identity theft. You can DETER identity theft through safeguarding your information. You can DETECT identity theft by monitoring your financial accounts and billing statements regularly. You can DEFEND identity theft by ordering our IDScreen
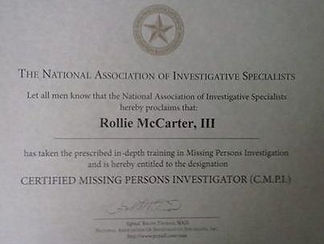
Rollie McCarter III - (413) 535-8653 - CALL/TEXT

Just about every minute of every day, decisions are made that can have a dramatic impact on the success or failure of your company, and none are more critical than hiring decisions. A simple, affordable, and extremely effective tool is the Employment Background Check, which is used to reduce the risks and liability associated with Negligent Hiring and retention.
Our Background Check Specialists can be very helpful to the company that is new to Background Checks, as well as those who are considering their current options. As more companies outsource operations, such companies who used their internal staff for activities, such as verification calls, found that it was more cost-effective to use our resources for these matters. While we are not authorized to offer legal advice regarding which searches you should conduct, we can educate you on the choices that exist and share which searches are most often requested.
CALL NOW, 413-535-8653, we would like an opportunity to demonstrate to you the exceptional quality of our service(s).

*RESUME' VERIFICATION*
Many job applicants and employees provide false education history, credentials, and employment history to appear more qualified. Unfortunately, companies may rely on this false information to provide compensation packages, promotions, and job responsibilities. Offering these benefits to an unqualified individual could waste time and money on training, negatively affect your company productivity, and increase your turnover rate. The best way to prevent these problems is to perform a full resume' verification with Rollie McCarter Investigative Services' thorough background checks to confirm work experience and education before making a "Negligent" hiring decision.
Student - Career - Professional - Executive
This search may include a Comprehensive background profile, Education verified (high school & college), Criminal, Civil, & Sex Offenses checked, Employment and Income verified, Online Profiles checked, References checked, Professional licenses & certifications verified. TAT (turn around time) 1 to 3 days. Search Fee: $100.00 - $400.00
Report Includes:
SSN VERIFICATION
ADDRESS HISTORY
CRIMINAL RECORD SEARCH
PAST EMPLOYMENT VERIFICATION
REFERENCE VERIFICATION
EDUCATION VERIFICATION
PROFESSIONAL LICENSE VERIFICATION
NATIONWIDE CRIMINAL SUPER SEARCH (INSTANT)
CLIENT agrees and understands that, in the event that SUBJECT refuses permission for RMIS to release their contact information to CLIENT, and/or indicates that they do not wish to renew any form of contact with CLIENT, then RMIS will under no circumstances release the SUBJECT'S contact information, or any other information pertaining to this investigation, or results of any part of this investigation to CLIENT, and the case shall be considered successful and closed. It is also understood that if this investigation reveals that the SUBJECT is now deceased or incarcerated, the case shall be considered successful and closed.
NOTE: We DO NOT locate Celebrities or Politicians

Hackers and online mischief makers often use a proxy or torrent that can allow these cyber bullies to mask their identity. These proxies can mask the real person’s identity by relaying their web traffic source IP address off computers outside of the realm and sphere of control of the U.S. legal system. These internet proxies often cause the apparent source of the defaming content or email message received to appear to originate from a source outside the U.S. that served as a proxy for their web traffic and content postings.
Here's what we can help with:
Counterfeit Website Identity Investigations
Cell Phone Traces & Landline Traces
PO BOX Traces / Vehicle Identity
Anonymous Poster Identity Tracking
Online Hacker Cyber Security Breach Investigations
Email Tracing, Authentication and Origin tracking
Social Media Suspect Profiling
Request Information